AD RPC (135)
MS Windows RPC is a protocol allowing applications on a Windows machine to communicate with applications on other machines, regardless of if they're on the same network or not. This port specifically facilitates the RPC endpoint mapper service.
The endpoint mapper helps clients identify the correct port on which an RPC service is running on a server. After initial contact on port 135, the server may assign a dynamic port for the specific RPC service you're interacting with.
rpcclient can be used to interact with the RPC interface.
Enumerate
nmap -sV -p 111 --script=rpcinfo $IP
impacket-rpcdump 10.10.11.174
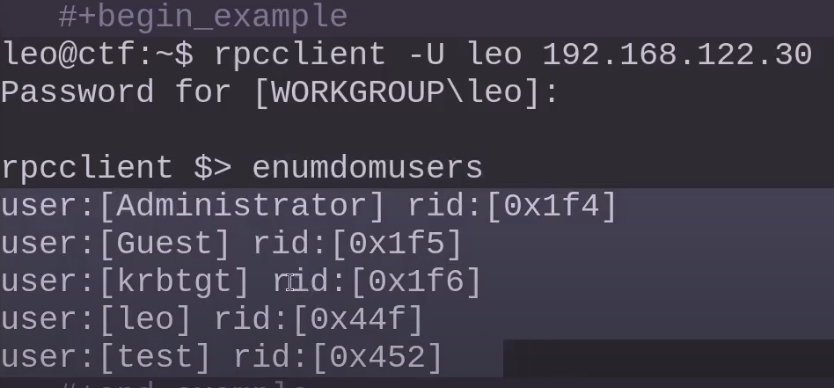
Rpcclient
rpcclient -U username%password ip_or_hostname
rpcclient -U 'V.Ventz%HotelCalifornia194!' 192.168.217.175
User enumeration (list all domain users)
enumdomusers
Query detailed info about a user (use RID from enumdomusers)
queryuser RID
List computers in the domain
enumcomputers
List all domain groups querygroup RID (Can be used to RID/SID bruteforce)
enumdomgroups
Get name from SID
lookupsids <SID>
Get name from RID
lookuprids <RID>
Get users in a group (older method)
querygroupmem RID
````
</div>
Get the domain SID
<div class="lang-general">
</div>
Get password policy info
<div class="lang-general">
</div>
Get password policy for a specific user
<div class="lang-general">
</div>
List shared folders
<div class="lang-general">
</div>
Server info
<div class="lang-general">
</div>
## **What Are SIDs and RIDs?**
**SID (Security Identifier)**: A unique identifier used by Windows systems to identify users, groups, computers, and other security principals.
- Format: `S-1-5-21-XXXXXXXXX-YYYYYYYYY-ZZZZZZZZZ-RID`
**RID (Relative Identifier)**: The final part of a SID.
- Example: In the SID `S-1-5-21-1004336348-1177238915-682003330-512`, the **`512`** is the RID.
- It identifies the specific object **relative to a domain** or local machine.
Together, SIDs and RIDs are fundamental to how **Windows manages security and access control.**
## **Bruteforce SIDs**
Attempt bruteforce with lookupsid
<div class="lang-general">
</div>
## **Bruteforce RIDs**
Try RID brute if you have found any RIDs
<div class="lang-general">